Cybersecurity Preparedness and Data Privacy Compliance
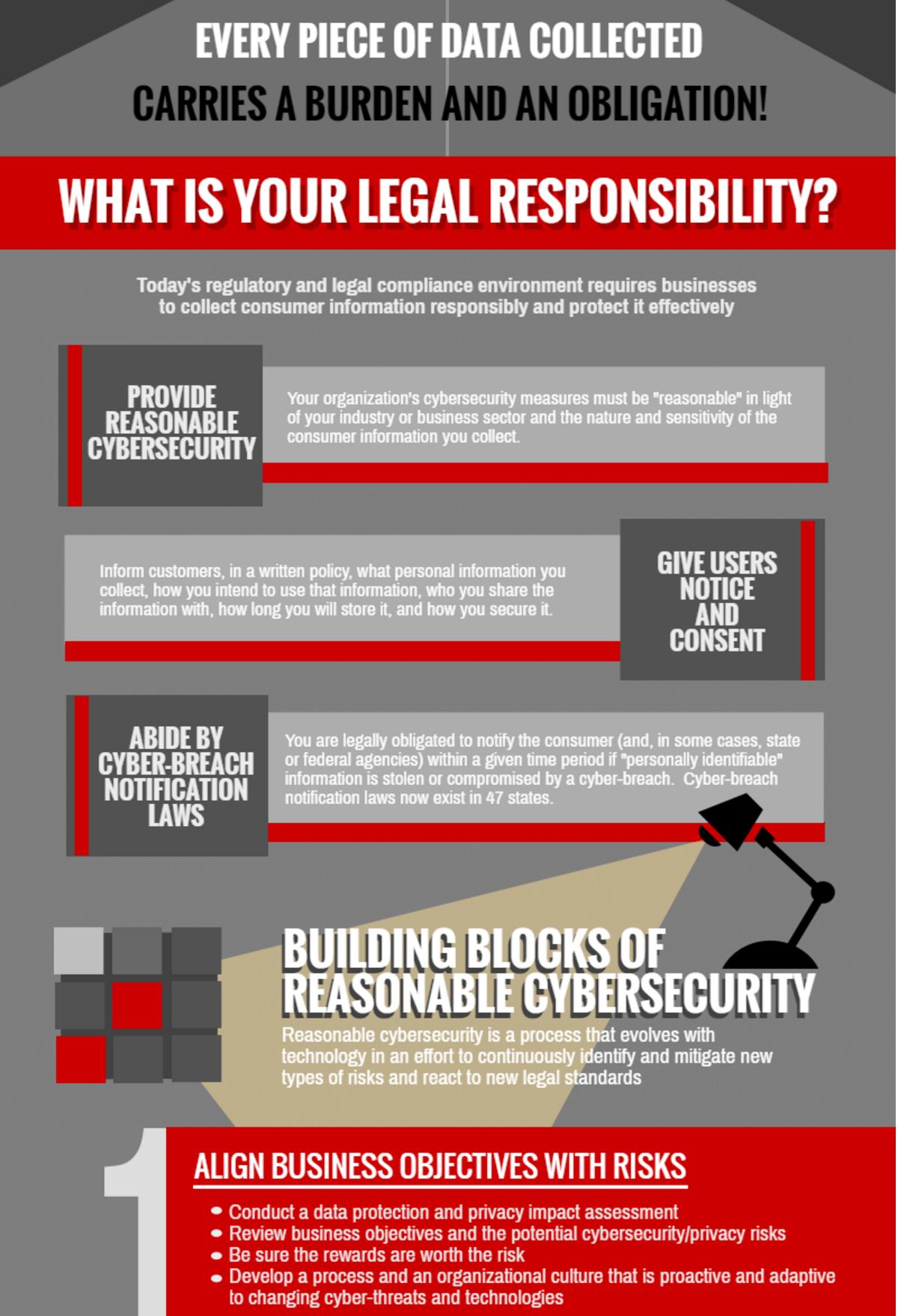
Instances of cybercrime are rising and the associated financial costs have exploded, not to mention the costs to an organization's reputation. Today's regulatory and legal compliance environment places a range of complex–and sometimes conflicting–burdens on businesses to responsibly collect consumer information and protect it effectively. The FTC, for example, requires companies to implement "reasonable cybersecurity" measures to protect consumer data. In regulated industries such as finance or commodities, more specific rules sometimes apply. Furthermore, almost every state has its own breach notification statute that requires organizations to notify consumers when their personal information has been stolen. However, state laws vary widely in detail, such as the definition of "personal information," whether a state agency also needs to be notified, and the length of the notice period.
In 2015, 71% of organizations experienced a cyberattack, and security breaches surged by 38% over 2014, which had been dubbed "the year of the breach."*
Many businesses also need to comply with the changing regulatory environment introduced by the EU General Data Protection Regulation, a complex regime governing data flows about individuals in the European Union. Businesses must fully comply with the GDPR, which substantially differs from the older "Directive," by May 2018. In addition, changing technological paradigms such as big data analytics and the Internet of Things, relying as they do on ever-expanding consumer data collection, dramatically increase the compliance burdens and the data exposure risk of cybersecurity breaches.
We counsel clients not only on the legal interpretations of privacy and cybersecurity laws, but also help them implement proactive, adaptive compliance and risk management programs that are based on sound technological approaches integrated to the very core of their product/service design. Our goal is to help you build a program that can not only reduce the risk of investigation and sanctions by state, federal, and international regulatory bodies, but also reduce the tangible, practical risk of an actual breach.
We can provide cybersecurity and data privacy compliance counseling and services to your organization using a variety of delivery and billing arrangements, from targeted hourly or flat-fee services to serving as your virtual, "outside" Chief Privacy Officer. Contact us for more information on our programs.

Some of the services we offer include:
- Counseling in privacy & data security laws
- Evaluation of cybersecurity risk
- Strategies for cybersecurity preparedness
- Incident response policies and procedures
- Compliance programs for data security
- Privacy audits
- Privacy-by-design programs and processes
- Privacy impact assessments (PIA)
- Privacy risk management for Big Data analytics and Internet of Things (IoT) products and services
- End-user privacy policies, licensing agreements, and terms of service (ToS)
- Cyber-risk mitigation strategies for cloud service/vendor agreements, technology licensing agreements, and M&A transactions
- Sharing information under CISA
- Counseling in GDPR and other international privacy/consumer-protection rules and regulations
At Labyrinth Law, our technology background in cybersecurity, coupled with knowledge of the applicable legal frameworks, places us in a unique position to help you evaluate your cyber-risk and target your cybersecurity budget where it will be most effective.
* CyberEdge Group, 2015 CyberThreat Defense Report
